TL;DR: Callstrike is the first enterprise platform built to simulate deepfake phishing attacks across voice, video, and messaging channels. It offers eight simulation types including AI vishing, human-in-the-loop voice cloning calls, deepfake conference hijacking on Zoom/Teams/Meet, WhatsApp spear phishing, callback phishing, and deepfake video generation. The entire platform runs from a browser with no GPU or desktop software required. It was built because no existing security awareness tool simulates the AI-powered social engineering attacks that enterprises now face.
Your training doesn't match the threat
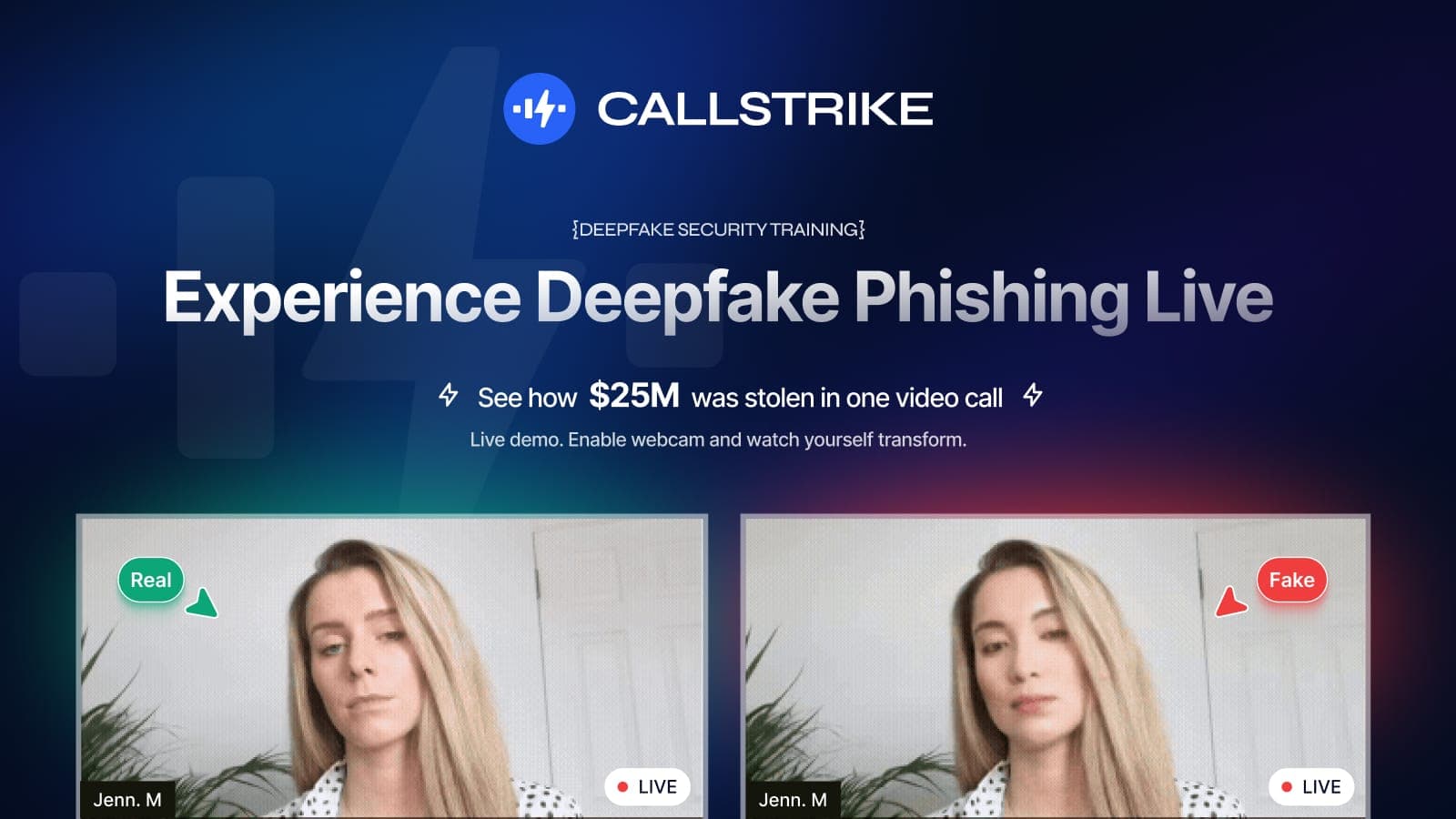
In 2025, a finance team at a multinational wired $25 million after a deepfake video call with someone they believed was their CFO. The attackers didn't send a phishing email. They didn't exploit a zero-day. They cloned a face, cloned a voice, and joined a video call.
Every major security awareness platform on the market today trains your people against one thing. Dodgy emails. Click-rate metrics. Simulated phishing links. That made sense ten years ago. But the threat has moved on. Attackers now clone voices from seconds of audio. They join your Zoom calls wearing your CEO's face. They send WhatsApp voice notes that sound exactly like your CFO asking for an urgent wire transfer.
We built Callstrike because nobody was simulating these attacks. Not one platform. The industry was stuck training people for yesterday's threat while ignoring the one that's already here.
Callstrike is the world's first enterprise deepfake phishing simulation platform, purpose-built for voice, video, and messaging attacks. This post covers why it exists and exactly what it does.
Eight simulation types across every channel attackers use
We didn't build a single feature and wrap it in a landing page. Callstrike is a full platform covering the entire spectrum of AI-powered social engineering, from automated voice calls to live deepfake video conferences. Here's each one.
AI Voice Phishing (Vishing)
Callstrike deploys automated outbound phone calls where AI voice bots impersonate executives, IT support staff, or external vendors. The bot follows a scenario you configure. An urgent password reset, a payment authorisation request, a compliance audit callback. It interacts with the target in real time.
This isn't a pre-recorded message. The AI adapts to responses, follows conversational branches, and applies social engineering pressure just like a real attacker would. You define the scenario, select the targets, and launch. The platform handles everything from call routing to response capture and reporting.
No specialised hardware. No telephony infrastructure to manage. It runs from your browser. See how AI vishing simulation works.
Human-in-the-Loop Spear Vishing
Automated bots are effective at scale, but the most dangerous real-world vishing attacks involve a human operator. Callstrike's human-in-the-loop mode combines deepfake voice cloning with a live operator who adapts dynamically to whatever the target says.
The operator speaks naturally while the platform transforms their voice in real time into the cloned voice of a specific executive. The result is a conversation that sounds exactly like your CEO or CFO, with the unpredictability and persuasion of a real human behind it.
This is the hardest test you can give your team. If they pass this, they're ready for what's actually coming. Learn more about human-in-the-loop vishing.
Callback Phishing
Not every voice attack starts with a phone call. Callback phishing starts with an email. A fake invoice, a security alert, an account suspension notice. It prompts the recipient to call a number. When they do, they reach a Callstrike AI voice bot running the social engineering scenario.
This simulates one of the fastest-growing attack vectors in enterprise fraud. The employee initiates the call themselves, which bypasses their instinct that incoming calls might be suspicious. It's a blind spot most organisations have never tested.
Conference Hijacking
This is the feature that changes the conversation entirely. Callstrike joins live Zoom, Microsoft Teams, and Google Meet sessions with face-swapped video and a cloned voice, simulating an attacker who has infiltrated your meeting as a trusted participant.
The platform uses a proprietary browser-based approach. No GPUs. No desktop software. No downloads. Enterprise-grade meeting impersonation delivered through a standard web browser.
Your team sees a familiar face and hears a familiar voice. The "participant" asks for sensitive information, requests an urgent action, or simply observes. The debrief afterwards is where the real training happens, when people realise they couldn't tell the difference. See how conference hijacking simulation works.
WhatsApp Spear Phishing
Corporate email isn't the only channel attackers use. Increasingly, executives and senior staff are targeted through personal messaging apps, WhatsApp in particular.
Callstrike launches personalised WhatsApp attacks using voice messages and video messages that impersonate known contacts. A voice note from the "CEO" asking a finance director to process a payment. A video message from "IT support" requesting login credentials.
This tests your team in the channel where their guard is lowest and where your security stack has zero visibility. Explore WhatsApp spear phishing simulation.
Voice Cloning (Voice Sniper)
At the core of several Callstrike simulations sits Voice Sniper, our voice cloning engine. It generates realistic voice replicas from just seconds of publicly available audio. A conference talk, a podcast appearance, a YouTube video. That's all an attacker needs, and it's all Callstrike needs to build the simulation.
Voice Sniper powers the AI vishing, human-in-the-loop, and conference hijacking modules. It's the engine that makes every voice-based simulation feel indistinguishable from the real person.
Deepfake Video Generation
Beyond live conference infiltration, Callstrike generates synthetic deepfake video content for training and awareness programmes. Pre-recorded deepfake videos showing executives delivering messages they never actually said, used in controlled training environments to demonstrate just how convincing the technology has become.
These videos are used in awareness briefings, board presentations, and compliance training. Seeing yourself deepfaked is the single most effective way to make someone take the threat seriously. Try the deepfake video maker.
Adaptive Training and Assessment
Simulation without follow-through is just a scare tactic. Every Callstrike simulation feeds into our adaptive training engine, which delivers personalised post-simulation modules to each employee based on how they performed.
The platform provides scenario-specific reviews, vulnerability analysis, interactive learning paths, and progress tracking over time. Managers get department-level risk heatmaps. Executives get trend analysis and compliance-ready reporting. See the deepfake awareness training module.
Why browser-based matters
Every feature listed above runs from a standard web browser. No GPU rigs. No desktop installations. No infrastructure to maintain. This was a deliberate engineering decision. If the platform is hard to deploy, enterprises won't use it at the frequency they need to.
Callstrike integrates with Okta, Azure AD, Google Workspace, and Slack for user management. It supports SSO/SAML, role-based access control, and department-level grouping. Deploy a campaign to your entire organisation in minutes, not weeks.
The threat has moved on from email. Attackers are cloning voices, hijacking video conferences, and sending deepfake WhatsApp messages. Callstrike exists because no other platform was willing to simulate what's actually happening. Eight simulation types, every channel, browser-based, no infrastructure overhead. If your security awareness programme only tests for phishing emails, it's testing for the wrong thing.
Frequently Asked Questions
Q: How is Callstrike different from existing phishing simulation platforms?
A: Traditional platforms like KnowBe4 and Proofpoint focus almost exclusively on email-based phishing. Callstrike simulates the next generation of attacks. AI voice calls, deepfake video conferences, voice cloning, WhatsApp phishing, and callback phishing. These are the threats attackers are already using that no other platform tests for.
Q: Do I need special hardware or infrastructure to run Callstrike?
A: No. The entire platform runs from a standard web browser. There are no GPU requirements, no desktop software to install, and no telephony infrastructure to manage. Callstrike's proprietary approach handles deepfake generation and voice cloning in the cloud.
Q: Is Callstrike safe to use in a live enterprise environment?
A: Yes. Every simulation is controlled, scoped, and fully auditable. Campaigns target only the employees you specify, and all interactions are logged for compliance and reporting. The platform is designed for enterprise security teams running authorised red team exercises and awareness programmes.
Q: How quickly can I get started?
A: Most organisations are running their first simulation within days of onboarding. User provisioning syncs with your existing identity provider (Okta, Azure AD, Google Workspace), and campaign setup is straightforward through the browser-based dashboard.
Share this article
Found it interesting? Don't hesitate to share it to your friends or colleagues